Proven Performance
Pre-vetted consultants with enterprise track records.
Advanced cybersecurity solutions powered by AI and expert intelligence. Safeguard your business against evolving threats with our comprehensive security ecosystem.
A premium experience with clear deliverables, fast communication, and measurable results.
Pre-vetted consultants with enterprise track records.
Start in days, not months—clear scopes and timelines.
Rapid triage, prioritized remediation, and follow-ups.
Executive summaries + technical detail your team can act on.
24/7 SOC monitoring, alerting, and incident response—delivered as a service.
Green Circle delivers fully managed cybersecurity services to protect organizations 24/7.
End-to-end security programs designed to reduce risk, improve visibility, and accelerate compliance.
Simulated attacks to uncover exploitable weaknesses across web, network, and cloud environments.
24/7 monitoring, alert triage, and proactive threat hunting using modern detection frameworks.
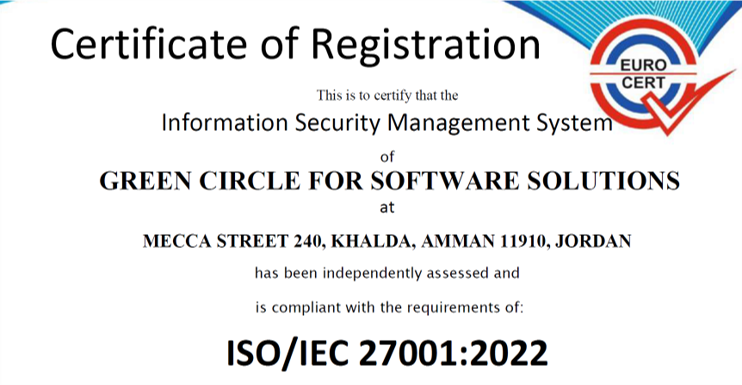
Practical governance, risk assessments, and compliance roadmaps aligned with ISO 27001, NIST, and local regulations.
LLM risk assessment, prompt-injection testing, data leakage controls, and AI governance aligned with best practices.
Innovating Security · Empowering Talent · Transforming Futures
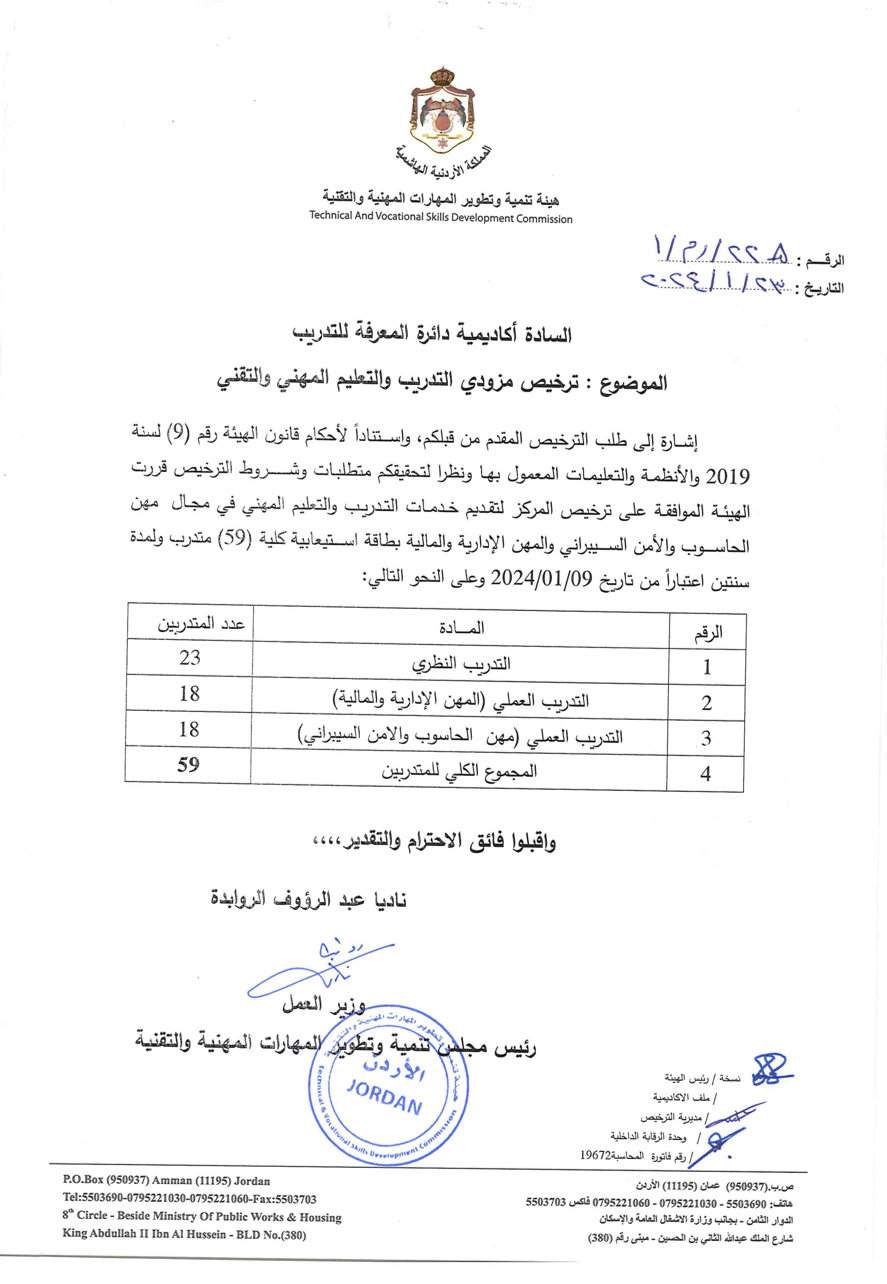
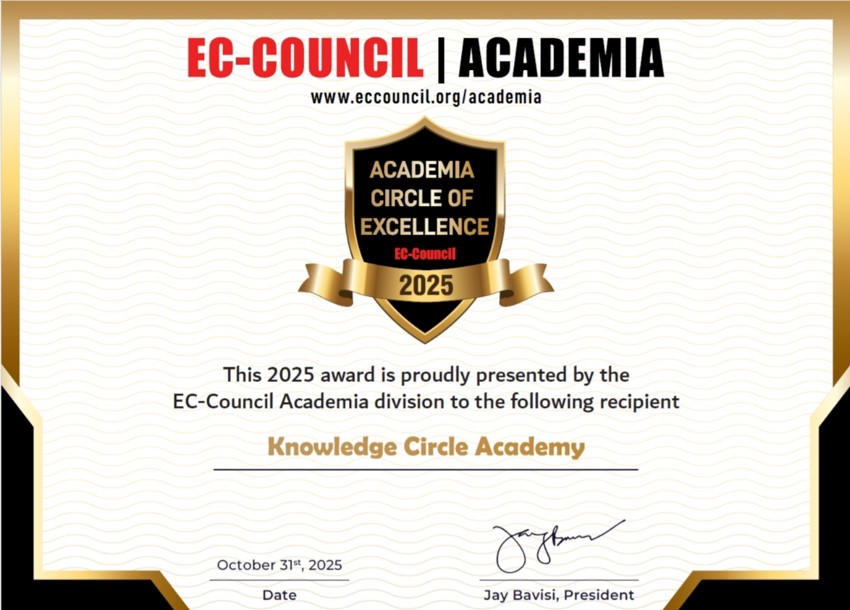
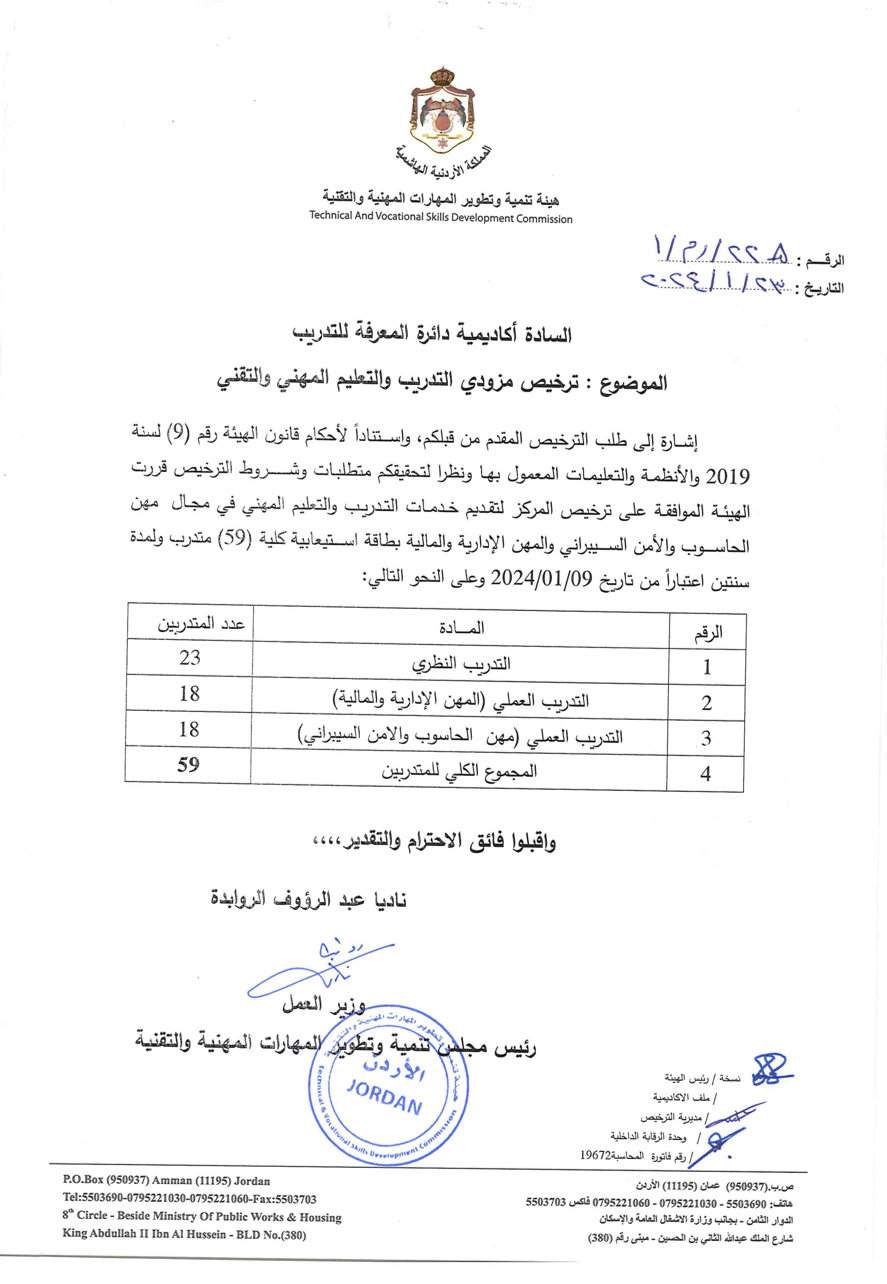
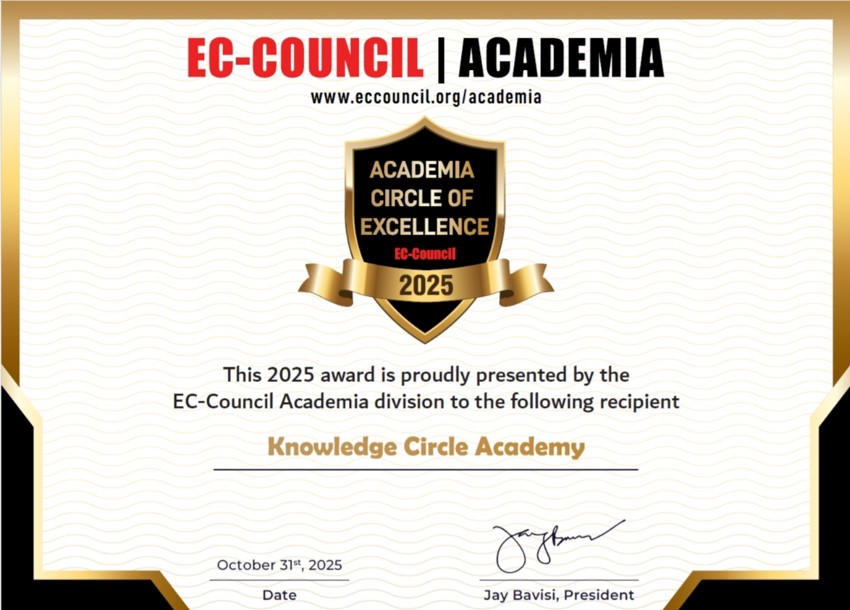
Licensed Authorized Academy — International & Local Accredited Courses
kca.edu.joAlumni & Open Education Platform
WorldCyberClub.comGig & Employment Engine
z2h.meCompetitions & Women in Cyber
ctfjo.comCSR · Schools & Youth Tech Transformation
DigitalJordan.orgUS-Based · Specialized AI Cyber Development Courses
Daience.UniversityUK-Based · AI Cyber Compliance · AI Act & GDPR Readiness
Irontic.AIGuide for Events & Activities · Hackathons & Tech Hub
eventsjordan.comCFYE · Q2Impact · Employment Support Network
86+ Global PartnersGreen Circle operates as a fully integrated Cybersecurity & AI ecosystem — combining R&D, enterprise managed services, and a continuous "Zero to Hero" talent pipeline to deliver comprehensive digital protection and solve the global cybersecurity skills gap.
From threat detection to incident response, we provide end-to-end cybersecurity solutions tailored to your needs.
24/7 monitoring and management of your security infrastructure with our expert SOC team. Real-time threat detection and rapid response.
Learn MoreIdentify vulnerabilities before attackers do with comprehensive security assessments.
ExploreCybersecurity & Digital Trust Ecosystem
Green Circle is a unified cybersecurity platform designed to deliver consulting, managed security, AI-driven protection, and workforce development through a single integrated ecosystem. We connect organizations, cybersecurity experts, young talent, and technology partners to build secure, resilient, and future-ready digital environments.
An integrated platform that connects services, innovation, and workforce development.
AI-powered threat detection, automated incident response, security agents & orchestration, AI governance, and LLM security controls—delivered as accelerators and advisory services.
Structured training tracks from entry-level to advanced, hands-on labs & CTFs, SOC/Blue Team, GRC, and AI security—aligned with market needs.
Capacity building through NGO programs, national initiatives, awareness campaigns, bootcamps, competitions, and scholarships—supporting sustainable cyber resilience.
Technology and community events by Green Circle in Jordan, connecting youth, experts, and companies with learning, innovation, and career opportunities.






















Highlights from our programs, events, and community engagement.






Customers, partners, Instant Partner, and accreditations that strengthen our impact.




























































































Strategic partners who collaborate with us to deliver secure and scalable solutions.








































Organizations and institutions supporting our mission and initiatives.







Official accreditations and certifications that validate our expertise and credibility.